- Products
- Advisors
- CMS Reviews
- Fair and Responsible Banking
- Community Reinvestment Act (CRA)
- Small Business Lending /Section 1071
- Crossing the $10B Threshold
- Fintech Compliance / Banking-as-a-Service
- Mortgage Support and HMDA Services
- Staff Augmentation/Managed Services
- Enterprise Risk Management
- Operational Reviews and Process Improvement
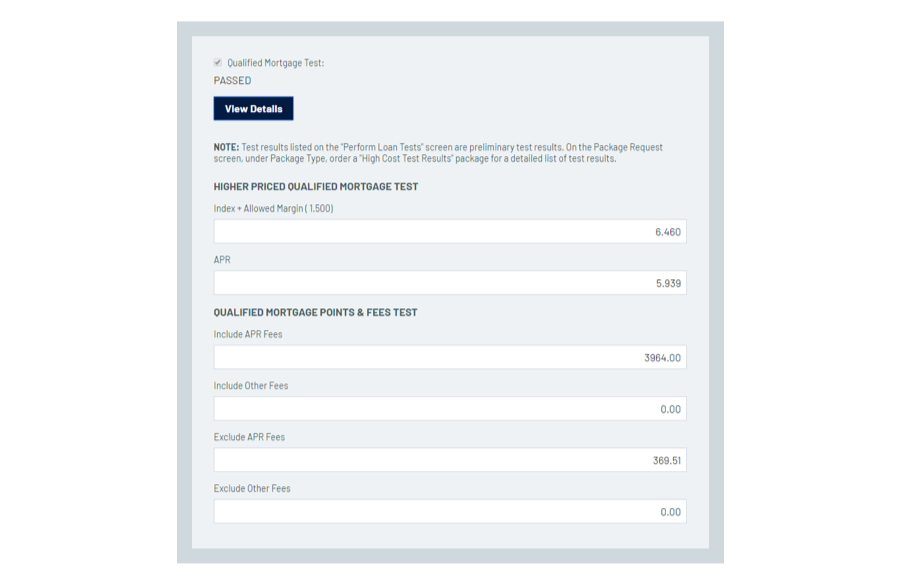
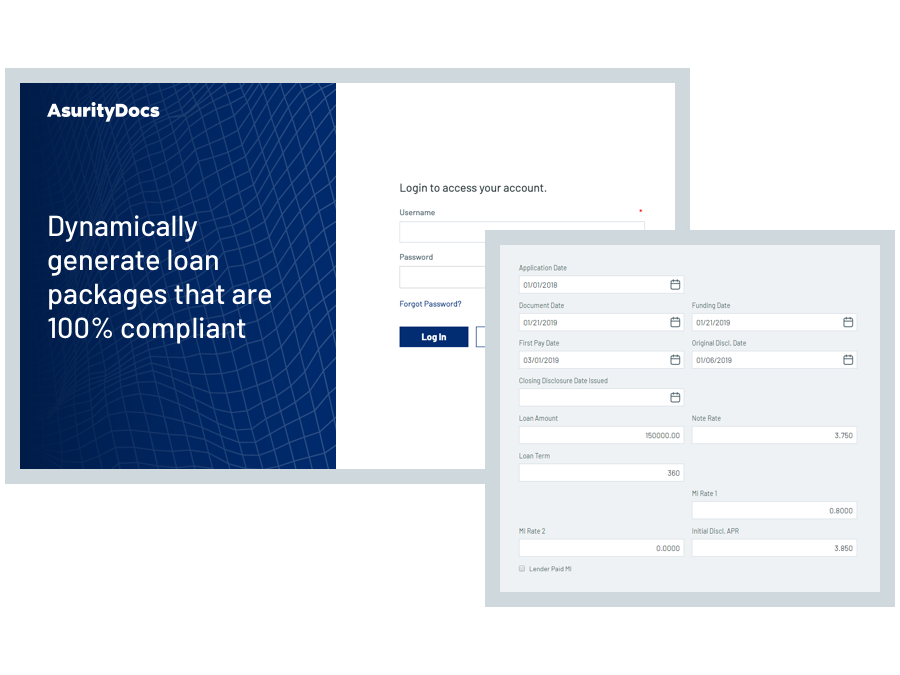
- Mortage Services
- Insights
- About Us